Scams are big business: every year, criminals steal billions of dollars from people of all ages. And when these criminals target older adults—which they often do—even more is at stake. Scammers steal retirement savings and even government benefits like Social Security with no remorse for their actions. Usually, they get away with it. And the personal and financial damage they cause can be devastating.
Consider this: In just 2024 alone, people age 60 and over collectively lost nearly $5 billion to cybercrime and other fraud.1 On average, these victims lost more than $32,000 each.
“This situation would be catastrophic for anyone,” said Jessica Johnston, Senior Director of NCOA’s Center for Economic Well-Being. “And especially so for those of us who don’t have decades of employment ahead to help recover a lifetime of savings.”
In this guide, you’ll learn about one of the internet’s oldest and most well-known scams: phishing. Armed with this knowledge, you can successfully fight back against criminals who want to steal your identity, your money, and your financial security.
What is phishing?
Phishing is a type of internet hoax that criminals love. These scammers use email, texting, social media, and other methods to steal personal data, like financial information or account passwords. And you can see where the unusual name comes from: because phishing uses attractive “bait” to lure people to websites and solicit their data under false pretenses.
Phishing is not the same as spam. Spam is just another term for junk mail and unwanted ads; phishing attacks are deliberate attempts to steal your information and use it in harmful ways.
How does phishing work?
All phishing scams share three things in common:
- They use electronic communications. Phishing attacks commonly happen through email, but criminals also try to contact you via text messages, social media accounts, voicemail, and even phone calls.
- They use your trust against you. Phishing works by convincing you that a fake email, text, phone call, or social media account is real. The scammer claims to be an individual or organization who’s familiar to you (a tactic known as social engineering), which makes the ruse seems credible.
- Their goal is theft. Phishing attacks are meant to steal sensitive personal information, such as passwords, bank details, Medicare and Social Security numbers, credit cards, and more.
All phishing attacks use carefully crafted appeals to get you to click on a link, download an attachment, or provide specific personal information. In some cases, scammers may even ask for payment. We’ve even seen scammers use vaccines as an excuse to steal Medicare numbers.
Some other common phishing attack examples include:
- A plea for help. With a goal of tugging at your heartstrings, the attacker sends you an email pretending to be a good friend or relative (like your grandchild). They claim to be in dire financial straits and urgently request that you send them money. How can cyber criminals so easily impersonate people you know? With social media, scammers have access to more of our personal information than ever before. This allows them to craft messages that often are very believable.
- A grand prize announcement. Scammers text you with congratulations and great news: you’ve won a very big prize, whether it's an irresistible travel package or free tickets to the event of the year. But first, in order to claim your award, you have to volunteer personal information or even pay an up-front fee.
- A notice that your bank account was compromised. Criminals impersonate someone from your financial institution and send an “urgent” notice to alert you about suspicious activity on your account. This notice directs you to click a link that brings you to a real-looking website (it’s fake), where you’re prompted to confirm your bank account details.
- A claim that the government is after you. Few things in life are as jarring as receiving a sternly worded notice from the Internal Revenue Service (IRS). Scammers know this, which is why many of them send phishing emails that look like they’re from the U.S. government. These emails typically have a threatening tone and mention big, scary penalties—“penalties” you can “avoid” if you simply offer the payment or personal data they demand. In some cases, criminals send these types of phishing emails and texts during tax season, lending them extra credibility. These scams offer a generous refund after you confirm your financial details.
Why does phishing work so well?
Emails, text messages, voicemail messages, and even voice calls are not authenticated. This means that—just like a postcard sent through the mail—there’s no real way to tell where they actually come from. That gives scammers plenty of freedom to mimic trusted people and brands in their communications.
Phishing is one of the most common and pervasive threats. In the FBI’s 2024 report on internet crime, it topped the list of complaints filed by people age 60 and over. At 23,252, that represents an astounding 814% increase over the previous year.1
The most accomplished phishers are very skilled at creating spoof (fake) emails and websites that are almost impossible to tell apart from the real thing. That includes the URL (website address) and security certificates. You may think you’re reading a credible message from a bank, online store, credit card company, or the government. Unless you’re paying very close attention, you might miss the signs of trickery until it’s too late.
How do you avoid phishing scams?
The good news: there are signs, and it’s possible to spot them. Knowing how to protect yourself against phishing emails and texts means knowing what to look for. While scammers constantly change their approaches to evade detection, there are certain red flags that can tip you off to trouble.
Some telltale signs of a phishing email or text message include:
- Offers that seem too good to be true
- High-pressure sales pitches that stress urgency
- Alerts about a problem with your account (like suspicious activity or outdated payment information)
- Links that are shortened or misspelled
- Emails that don't address you by name
- Messages with poor grammar and spelling
- Direct requests or demands for payment
- Requests to confirm personal information
The best defense against a phishing scam is to verify with the person or organization(s) who sent the email or message before clicking on anything.
Remember that you can never be 100% certain that the sender of an email, text message, voicemail, or phone call is who they say they are. That’s why it’s important to approach every communication with a healthy dose of skepticism.
Personal cybersecurity best practices to keep in mind
- Don’t click on any links found within emails or text messages if you didn’t initiate the original message. Be suspicious of all unsolicited and/or unexpected communications.
- Do navigate to trusted websites directly by typing the web address into the browser address bar yourself. Don’t click through a link.
- Do verify website security certificates by clicking the small padlock icon in the left corner of the browser address bar. Make sure the URL begins with “HTTPS.” An HTTPS connection is protected by a special type of security technology, which means that any information you send through the website is kept private.
- Don’t send personal information in email or text messages. Again, this information is not secure, and you can’t be sure who the recipient is.
- Don’t ever give out personal information over the phone during calls you didn’t make yourself. Always double-check to make sure you’re using the correct phone number of the person or business you’re trying to contact.
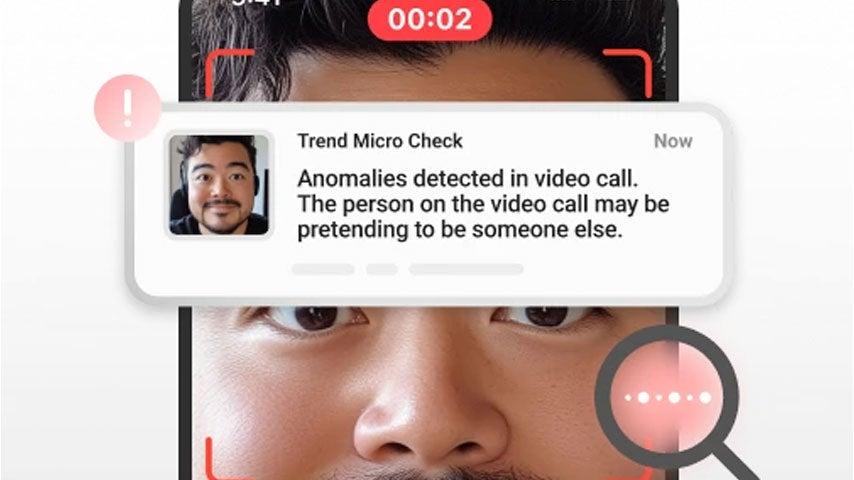
When it comes to preventing phishing scams, education is a powerful way to protect yourself. Another is to install reputable antivirus software on your devices. Many of these software programs contain an anti-phishing tool that detects and blocks phishing attempts before they reach you. There are a number of trusted options available for free on the web.
Source
1. Federal Bureau of Investigation. Internet Crime Report 2024. Found on the internet at https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf